About Apple security updates
Security Update 2017-006 is recommended for all users and improves the security of OS X. This update includes the following improvements: afclip. Available for: macOS Sierra 10.12.5. MacOS Sierra 10.12.5, Security Update 2017-002 El Capitan, and Security Update 2017-002 Yosemite. MacOS Sierra 10.12.4, OS X El Capitan 10.11.6, and OS X Yosemite 10.10.5. IPhone 5 and later, iPad 4th generation and later, and iPod touch 6th generation. Apple Music 2.0 for Android. Android version 4.3. MacOS Sierra (version 10.12) is the thirteenth major release of macOS (previously known as OS X and Mac OS X), Apple Inc.' S desktop and server operating system for Macintosh computers. The name 'macOS' stems from the intention to uniform the operating system's name with that of iOS, watchOS and tvOS. Sierra is named after the Sierra Nevada mountain range in California and Nevada.
Recent releases are listed on the Apple security updates page. Apple security documents reference vulnerabilities by CVE-ID when possible. For more information about security, see the Apple Product Security page. MacOS Mojave 10.14.4, Security Update 2019-002 High Sierra, Security Update 2019-002 Sierra.
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
For more information about security, see the Apple Product Security page. You can encrypt communications with Apple using the Apple Product Security PGP Key.
Apple security documents reference vulnerabilities by CVE-ID when possible.
macOS High Sierra 10.13.1, Security Update 2017-001 Sierra, and Security Update 2017-004 El Capitan
Released October 31, 2017
apache
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Multiple issues in Apache
Description: Multiple issues were addressed by updating to version 2.4.27.
CVE-2016-0736
CVE-2016-2161
CVE-2016-5387
CVE-2016-8740
CVE-2016-8743
CVE-2017-3167
CVE-2017-3169
CVE-2017-7659
CVE-2017-7668
CVE-2017-7679
CVE-2017-9788
CVE-2017-9789
Entry updated November 14, 2017
APFS
Available for: macOS High Sierra 10.13
Impact: A malicious Thunderbolt adapter may be able to recover unencrypted APFS filesystem data
Description: An issue existed in the handling of DMA. This issue was addressed by limiting the time the FileVault decryption buffers are DMA mapped to the duration of the I/O operation.
CVE-2017-13786: Dmytro Oleksiuk
Entry updated November 10, 2017
APFS
Available for: macOS High Sierra 10.13
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13800: Sergej Schumilo of Ruhr-University Bochum
AppleScript
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Decompiling an AppleScript with osadecompile may lead to arbitrary code execution
Description: A validation issue was addressed with improved input sanitization.
CVE-2017-13809: bat0s
Entry updated November 10, 2017
ATS
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: A memory corruption issue was addressed with improved input validation.
CVE-2017-13820: John Villamil, Doyensec
Audio
Available for: macOS Sierra 10.12.6
Impact: Parsing a maliciously crafted QuickTime file may lead to an unexpected application termination or arbitrary code execution
Description: A memory consumption issue was addressed with improved memory handling.
CVE-2017-13807: Yangkang (@dnpushme) of Qihoo 360 Qex Team
Entry updated January 22, 2019
CFNetwork
Available for: OS X El Capitan 10.11.6, and macOS Sierra 10.12.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13829: Niklas Baumstark and Samuel Gro working with Trend Micro's Zero Day Initiative
CVE-2017-13833: Niklas Baumstark and Samuel Gro working with Trend Micro's Zero Day Initiative
Entry added November 10, 2017
CFString
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2017-13821: Australian Cyber Security Centre – Australian Signals Directorate
CoreText
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6
Impact: Processing a maliciously crafted font file may lead to arbitrary code execution
Description: A memory consumption issue was addressed with improved memory handling.
CVE-2017-13825: Australian Cyber Security Centre – Australian Signals Directorate
Entry updated November 16, 2018
curl
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Uploading using TFTP to a maliciously crafted URL with libcurl may disclose application memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2017-1000100: Even Rouault, found by OSS-Fuzz
curl
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Processing a maliciously crafted URL with libcurl may cause unexpected application termination or read process memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2017-1000101: Brian Carpenter, Yongji Ouyang
Dictionary Widget
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Searching pasted text in the Dictionary widget may lead to compromise of user information
Description: A validation issue existed which allowed local file access. This was addressed with input sanitization.
CVE-2017-13801: xisigr of Tencent's Xuanwu Lab (tencent.com)
file
Available for: macOS Sierra 10.12.6
Impact: Multiple issues in file
Description: Multiple issues were addressed by updating to version 5.31.
CVE-2017-13815: found by OSS-Fuzz
Entry updated October 18, 2018
Fonts
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Rendering untrusted text may lead to spoofing
Description: An inconsistent user interface issue was addressed with improved state management.
CVE-2017-13828: Leonard Grey and Robert Sesek of Google Chrome
Entry updated November 10, 2017
fsck_msdos
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13811: V.E.O. (@VYSEa) of Mobile Advanced Threat Team of Trend Micro
Entry updated November 2, 2017
HFS
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13830: Sergej Schumilo of Ruhr-University Bochum
Heimdal
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An attacker in a privileged network position may be able to impersonate a service
Description: A validation issue existed in the handling of the KDC-REP service name. This issue was addressed with improved validation.
CVE-2017-11103: Jeffrey Altman, Viktor Duchovni, and Nico Williams
Entry updated January 22, 2019
HelpViewer
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: A quarantined HTML file may execute arbitrary JavaScript cross-origin
Description: A cross-site scripting issue existed in HelpViewer. This issue was addressed by removing the affected file.
CVE-2017-13819: Filippo Cavallarin of SecuriTeam Secure Disclosure
Entry updated November 10, 2017
ImageIO
Available for: macOS Sierra 10.12.6
What Is The Latest Update For Macos High Sierra
Impact: Processing a maliciously crafted image may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2017-13814: Australian Cyber Security Centre – Australian Signals Directorate
Entry updated November 16, 2018
ImageIO
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6
Impact: Processing a maliciously crafted image may lead to a denial of service
Description: A memory corruption issue was addressed with improved input validation.
CVE-2017-13831: Glen Carmichael
Entry updated April 3, 2019
IOAcceleratorFamily
Available for: macOS Sierra 10.12.6
Impact: A malicious application may be able to elevate privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13906
Entry added October 18, 2018
Kernel
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: A local user may be able to leak sensitive user information
Description: A permissions issue existed in kernel packet counters. This issue was addressed with improved permission validation.
CVE-2017-13810: Zhiyun Qian of University of California, Riverside
Entry updated January 22, 2019
Kernel
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: A local user may be able to read kernel memory
Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
CVE-2017-13817: Maxime Villard (m00nbsd)
Kernel
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2017-13818: The UK's National Cyber Security Centre (NCSC)
CVE-2017-13836: Vlad Tsyrklevich
CVE-2017-13841: Vlad Tsyrklevich
CVE-2017-13840: Vlad Tsyrklevich
CVE-2017-13842: Vlad Tsyrklevich
CVE-2017-13782: Kevin Backhouse of Semmle Ltd.
Entry updated June 18, 2018
Kernel
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13843: an anonymous researcher, an anonymous researcher
Kernel
Available for: macOS Sierra 10.12.6
Impact: Processing a malformed mach binary may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved validation.
CVE-2017-13834: Maxime Villard (m00nbsd)
Entry updated January 22, 2019
Kernel
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13799: Lufeng Li of Qihoo 360 Vulcan Team
Entry updated November 10, 2017
Kernel
Available for: macOS High Sierra 10.13
Impact: A malicious application may be able to learn information about the presence and operation of other applications on the device.
Description: An application was able to access process information maintained by the operating system unrestricted. This issue was addressed with rate limiting.
CVE-2017-13852: Xiaokuan Zhang and Yinqian Zhang of The Ohio State University, Xueqiang Wang and XiaoFeng Wang of Indiana University Bloomington, and Xiaolong Bai of Tsinghua University
Entry added November 10, 2017, updated January 22, 2019
libarchive
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6
Impact: Unpacking a maliciously crafted archive may lead to arbitrary code execution
Description: Multiple memory corruption issues existed in libarchive. These issues were addressed with improved input validation.
CVE-2017-13813: found by OSS-Fuzz
Entry updated November 16, 2018, updated January 22, 2019
libarchive
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Unpacking a maliciously crafted archive may lead to arbitrary code execution
Description: Multiple memory corruption issues existed in libarchive. These issues were addressed with improved input validation.
CVE-2017-13812: found by OSS-Fuzz
Entry updated January 22, 2019
libarchive
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2016-4736: Proteas of Qihoo 360 Nirvan Team
Entry updated December 21, 2017
libxml2
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6
Impact: Processing maliciously crafted XML may lead to an unexpected application termination or arbitrary code execution
Description: A null pointer dereference was addressed with improved validation.
CVE-2017-5969: Gustavo Grieco
Entry added October 18, 2018
libxml2
Available for: OS X El Capitan 10.11.6
Impact: Processing maliciously crafted XML may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2017-5130: an anonymous researcher
CVE-2017-7376: an anonymous researcher
Entry added October 18, 2018
libxml2
Available for: macOS Sierra 10.12.6
Impact: Processing maliciously crafted XML may lead to an unexpected application termination or arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2017-9050: Mateusz Jurczyk (j00ru) of Google Project Zero
Entry added October 18, 2018
libxml2
Available for: macOS Sierra 10.12.6
Impact: Processing maliciously crafted XML may lead to an unexpected application termination or arbitrary code execution
Description: A use after free issue was addressed with improved memory management.

CVE-2017-9049: Wei Lei and Liu Yang - Nanyang Technological University in Singapore
Entry added October 18, 2018
LinkPresentation
Available for: macOS High Sierra 10.13
Impact: Visiting a malicious website may lead to address bar spoofing
Description: An inconsistent user interface issue was addressed with improved state management.
CVE-2018-4390: Rayyan Bijoora (@Bijoora) of The City School, PAF Chapter
CVE-2018-4391: Rayyan Bijoora (@Bijoora) of The City School, PAF Chapter
Entry added November 16, 2018
Login Window
Available for: macOS High Sierra 10.13
Impact: The screen lock may unexpectedly remain unlocked
Description: A state management issue was addressed with improved state validation.
CVE-2017-13907: an anonymous researcher
Entry added October 18, 2018
Open Scripting Architecture
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Decompiling an AppleScript with osadecompile may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13824: an anonymous researcher
PCRE
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Multiple issues in pcre
Description: Multiple issues were addressed by updating to version 8.40.
CVE-2017-13846
Postfix
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Multiple issues in Postfix
Description: Multiple issues were addressed by updating to version 3.2.2.
CVE-2017-10140: an anonymous researcher
Entry updated November 17, 2017
Quick Look
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2017-13822: Australian Cyber Security Centre – Australian Signals Directorate
Quick Look
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Parsing a maliciously crafted office document may lead to an unexpected application termination or arbitrary code execution
Description: A memory consumption issue was addressed with improved memory handling.
CVE-2017-7132: Australian Cyber Security Centre – Australian Signals Directorate
Entry updated January 22, 2019
QuickTime
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2017-13823: Xiangkun Jia of Institute of Software Chinese Academy of Sciences
Entry updated November 10, 2017
Remote Management
Available for: macOS Sierra 10.12.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13808: an anonymous researcher
Sandbox
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-13838: Alastair Houghton
Entry updated November 10, 2017
Security
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: An authorization issue was addressed with improved state management.
CVE-2017-7170: Patrick Wardle of Synack
Entry added January 11, 2018
Security
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: A malicious application can extract keychain passwords
Description: A method existed for applications to bypass the keychain access prompt with a synthetic click. This was addressed by requiring the user password when prompting for keychain access.
CVE-2017-7150: Patrick Wardle of Synack
Entry added November 17, 2017
SMB
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6
Impact: A local attacker may be able to execute non-executable text files via an SMB share
Description: An issue in handling file permissions was addressed with improved validation.
CVE-2017-13908: an anonymous researcher
Entry added October 18, 2018
StreamingZip
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: A malicious zip file may be able modify restricted areas of the file system
Description: A path handling issue was addressed with improved validation.
CVE-2017-13804: @qwertyoruiopz at KJC Research Intl. S.R.L.
tcpdump
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6
Impact: Multiple issues in tcpdump
Description: Multiple issues were addressed by updating to version 4.9.2.
CVE-2017-11108
CVE-2017-11541
CVE-2017-11542
CVE-2017-11543
CVE-2017-12893
CVE-2017-12894
CVE-2017-12895
CVE-2017-12896
CVE-2017-12897
CVE-2017-12898
CVE-2017-12899
CVE-2017-12900
CVE-2017-12901
CVE-2017-12902
CVE-2017-12985
CVE-2017-12986
CVE-2017-12987
CVE-2017-12988
CVE-2017-12989
CVE-2017-12990
CVE-2017-12991
CVE-2017-12992
CVE-2017-12993
CVE-2017-12994
CVE-2017-12995
CVE-2017-12996
CVE-2017-12997
CVE-2017-12998
CVE-2017-12999
CVE-2017-13000
CVE-2017-13001
CVE-2017-13002
CVE-2017-13003
CVE-2017-13004
CVE-2017-13005
CVE-2017-13006
CVE-2017-13007
CVE-2017-13008
CVE-2017-13009
CVE-2017-13010
CVE-2017-13011
CVE-2017-13012
CVE-2017-13013
CVE-2017-13014
CVE-2017-13015
CVE-2017-13016
CVE-2017-13017
CVE-2017-13018
CVE-2017-13019
CVE-2017-13020
CVE-2017-13021
CVE-2017-13022
CVE-2017-13023
CVE-2017-13024
CVE-2017-13025
CVE-2017-13026
CVE-2017-13027
CVE-2017-13028
CVE-2017-13029
CVE-2017-13030
CVE-2017-13031
CVE-2017-13032
CVE-2017-13033
CVE-2017-13034
CVE-2017-13035
CVE-2017-13036
CVE-2017-13037
CVE-2017-13038
CVE-2017-13039
CVE-2017-13040
CVE-2017-13041
CVE-2017-13042
CVE-2017-13043
CVE-2017-13044
CVE-2017-13045
CVE-2017-13046
CVE-2017-13047
CVE-2017-13048
CVE-2017-13049
CVE-2017-13050
CVE-2017-13051
CVE-2017-13052
CVE-2017-13053
CVE-2017-13054
CVE-2017-13055
CVE-2017-13687
CVE-2017-13688
CVE-2017-13689
CVE-2017-13690
CVE-2017-13725
Wi-Fi
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An attacker in Wi-Fi range may force nonce reuse in WPA unicast/PTK clients (Key Reinstallation Attacks - KRACK)
Description: A logic issue existed in the handling of state transitions. This was addressed with improved state management.
CVE-2017-13077: Mathy Vanhoef of the imec-DistriNet group at KU Leuven
CVE-2017-13078: Mathy Vanhoef of the imec-DistriNet group at KU Leuven
Entry updated November 3, 2017
Wi-Fi
Available for: macOS High Sierra 10.13, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An attacker in Wi-Fi range may force nonce reuse in WPA multicast/GTK clients (Key Reinstallation Attacks - KRACK)
Description: A logic issue existed in the handling of state transitions. This was addressed with improved state management.
CVE-2017-13080: Mathy Vanhoef of the imec-DistriNet group at KU Leuven
Entry updated November 3, 2017
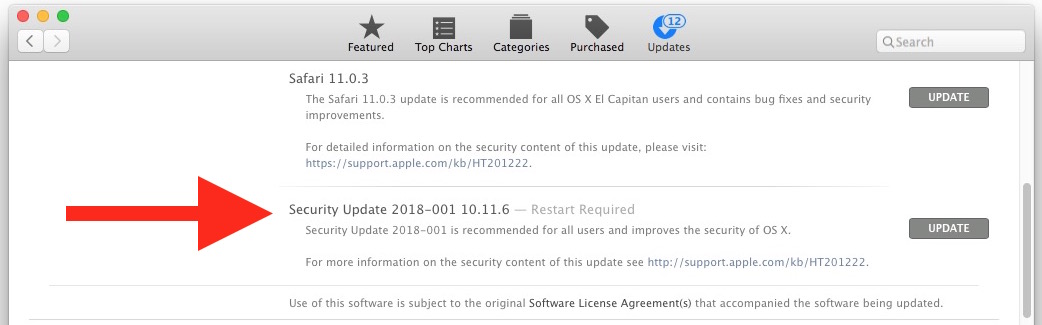
Installing security updates is one of the best ways to protect your Mac against online attacks. Apple regularly releases security patches for various macOS versions to fix known vulnerabilities.
Last May 13, Apple released Security Update 2019-003 for Sierra and High Sierra, together with the macOS Mojave 10.14.5 update. The macOS Mojave 10.14.5 update is around 2.8 GB, while Security Update 2019-003 is 1.9 GB in size. These updates were released to address vulnerabilities in various products. Safari 12.1.1 was also included in this security update.
Here are some of the changes High Sierra Security Update 2019-003 brings:
- AirPlay 2 support for compatible Smart TVs
- Improvements to the Apple News+ app
- Lower audio latency for MacBook Pro 2018
- Fixed a bug in OmniOutliner and OmniPlan
- Disabling of accessories using unsecured Bluetooth connections
- Fixed an issue with a user account password reset after using a personal recovery key (PRK) in FileVault
- Fixed an App Firewall bug
- Fixed a bypass for Gatekeeper checks
- Fixed vulnerabilities related to crafted audio and video files
- Fixed issues with Disk Images
- Fixed authentication issues with EFI
- Fixed three kernel bugs
- Fixed four SQLite bugs
- Fixed multiple bugs in WebKit
High Sierra users can download the security update via the App Store or get the standalone installer here.
The installation should be a straightforward process, but several users reported issues with High Sierra Security Update 2019-003. According to the reports, Security Update 2019-003 is causing problems on Mac — from slow bootup to crashing apps to install failures.
Pro Tip: Scan your Mac for performance issues, junk files, harmful apps, and security threats
that can cause system issues or slow performance.
Macos Sierra Security Updates
Special offer. About Outbyte, uninstall instructions, EULA, Privacy Policy.
Other users had to install the update multiple times because the security features were not applied. In a case like theirs, the installation seems successful and the user is prompted to reboot, but then the user is prompted to install the update again after the restart. Some users can’t even boot at all.
Upgrade Macos Sierra
The issues are different for each user, but the common denominator is that these problems started right after they installed the new High Sierra update. This problem has caused a lot of frustration among Mac users who installed the update, but Apple has yet to comment on the issue. There is a chance that this security update for High Sierra that is causing issues might be buggy so we’ll have to wait for Apple to acknowledge it.
Reasons Why Security Update 2019-003 Is Causing Problems on Mac
Security updates causing various issues on Mac are not a new thing. These issues with High Sierra Security Update 2019-003 can be caused by a lot of factors. Here are some of the possible reasons why you’re experiencing problems after installing the update:
- Failed or incomplete update installation
- Wonky third-party apps
- Not enough storage space
- Hard disk problems
We’ve listed down some troubleshooting methods below to fix these issues after installing the security update. This guide includes general troubleshooting steps and some problem-specific fixes. Depending on the problem you are having, you might need to try a combination of these solutions to see which one would work.
How to Fix Problems Caused by High Sierra Security Update 2019-003
Before you start, it is always advisable to run some maintenance steps to prepare your Mac for the troubleshooting process. Run your antivirus software to check if you have malicious software running on your computer. Delete all infected files to make sure you get rid of the virus or malware completely.
Delete apps and files that you no longer need and use Outbyte MacRepair to get rid of junk files. After cleaning up your computer, restart it and try the methods below one by one.
Step 1: Run Apple Diagnostics or Apple Hardware Test
This diagnostic tool is built into every macOS device to check for issues with your hardware. For Macs released from 2013 or later, the tool is named Apple Diagnostics, while older Macs have the Apple Hardware Test. You need to run this utility to rule out any hardware problems.
To run Apple Diagnostics:
- Restart your Mac, then press and hold the D button while starting up.
- Apple Diagnostics will start automatically and scan your computer for problems.
- Once the process has been completed, you’ll be provided with a list of problems detected.
If you see a major problem during your scan, seek out Apple Support or send your Mac to a repair center to get it fixed. If there are no issues, proceed with the other fixes below.
Step 2: Reset NVRAM
Your Mac’s NVRAM stores information even when the power is turned off so that you don’t have to fetch it again when you resume computer use. However, some data could get corrupted during the update process and cause issues for your Mac. Resetting the NVRAM should easily fix this.
To reset NVRAM, restart your Mac and hold down Command + Option + P + R. Your computer should restart again after the NVRAM has been reset. After rebooting, check if the issues caused by the security update have been fixed.
Step 3: Check Storage Space
Another reason your update is failing and causing issues on your Mac is because of insufficient storage space. The High Sierra security update 2019-003 is a big file, so make sure you have enough room for it. Tech experts recommend clearing up at least 10 GB of space every time you install updates to avoid problems. Deleting your unused apps and junk files should clear up enough space for your updates.
Step 4: Install in Safe Mode
If you’re having problems booting up in normal mode, you can boot into Safe Mode instead. Just hold the Shift key when your computer is booting up to launch Safe Mode. Open the Mac App Store and install the High Sierra security update 2019-003 from there. Reboot into normal mode and see if the issues still persist.
Step 5: Reinstall macOS
If the update-related problems don’t go away after doing all the steps above, your last option is to reinstall macOS. Don’t worry because you can do this without wiping out your data. Reinstalling your computer’s operating system will overwrite all Apple system files and replace any problematic ones that may be causing your computer issues.
To reinstall macOS using Recovery Mode:
Macos High Sierra Security Update Download
- Hold down Command + R while restarting your Mac.
- When the macOS Utilities window appears, click Reinstall macOS.
- Click Continue.
- Follow the onscreen instructions to choose the hard drive you want to install macOS on and start the installation.
Macos High Sierra Upgrade
Wait for the installation to be completed, then check if the previous issues still remain.
Macos Sierra 10.12.6 Security Update
Summary
Installing security updates, such as 2019-003, is crucial in protecting your Mac against attacks because they fix bugs and vulnerabilities that could be exploited by attackers. If installing this security update for High Sierra is causing issues for your Mac, you can follow the guide above to resolve these issues while keeping your macOS updated.
See more information about Outbyte and uninstall instructions. Please review EULA and Privacy Policy.
